
China’s bizarre addiction to the outside appearance of American-made fighter jets, warships and tanks is out of control. Chinese defence experts told CCTV that Chinese defence companies and the military need to get out of the mentality of appearance rather than focus on what inside the plane matters most for China, for example, avionics, sensors and armaments.
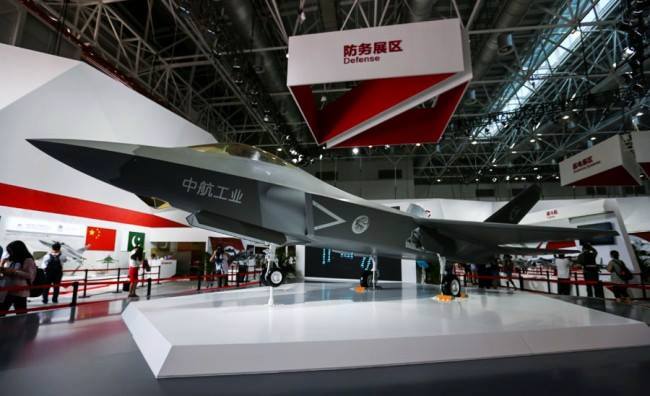
Known as the FC-31 fourth-generation multi-purpose medium fighter, the export variant of the J-31 fighter was also displayed at the Zhuhai Air Show 2014.
The Shenyang J-31 (F-60) is a multi-role, twin-engine fighter aircraft being manufactured for the People’s Liberation Army Air Force (PLAAF) by Shenyang Aircraft Corporation, an affiliate of Aviation Industry Corporation of China (AVIC). It is the second attempt for China to build a domestic fighter jet after the J-20.
The J-31 fighter jet is intended to provide advanced defense capabilities in close-air support, aerial bombing and air interdiction operations. It can also perform suppression of enemy air defenses and can be used as a carrier-based fighter on aircraft carriers. Initial operational capability of the aircraft is expected in 2020.
J-31 prototype (31001)
The J-31 prototype (31001) performed its maiden flight on 31 October 2012. A model of the aircraft was exhibited at the China International Aviation & Aerospace Exhibition (Airshow China) held in Zhuhai in November 2012. The J-31 prototype made a test flight during the Zhuhai Air Show in November 2014.
J-31 prototype (31001)
The FC-31’s airframe and control surfaces are similar to those of J-31 but will be outfitted with angled vertical stabilisers, two large internal payload bays and an estimated payload capacity of 2,268kg. It can also be attached with electro-optical and sensor system (EOSS) pod and infrared search-and-track sensors below the nose.
Cyber Espionage
The Chengdu tried to adopt Electro-Optical Targeting System (EOTS) in terms of shape and placement. In 2007, Chinese hackers allegedly stole technical documents related to the F-35 from Lockheed Martin.
Daniel Coats, in a congressional testimony published in May 2017, named Russia, China, Iran and North Korea as “Cyber Threat Actors.”
“Adversaries will continue to use cyber operations to undermine U.S. military and commercial advantage by hacking into U.S. defense industry and commercial enterprises in pursuit of scientific, technical, and business information,” Coats stated.
“Examples include theft of data on the F-35 Joint Strike Fighter, the F-22 Raptor fighter jet, and the MV-22 Osprey. In addition, adversaries often target personal accounts of government officials and their private-sector counterparts. This espionage reduces cost and accelerates the development of foreign weapon systems, enables foreign reverse-engineering and countermeasures development, and undermines U.S. military, technological, and commercial advantage.”
Putter Panda
The group is known as “Putter Panda” by security researchers, and Crowdstrike believes it is located in Shanghai, China, housed in buildings belonging to the People’s Liberation Army or PLA.
Putter Panda is thought to have been active since 2007 at least. It targets American and European defence and satellite and aerospace industries, using exploits in popular applications such as Adobe Reader and Microsoft’s Office productivity suite.
Stealing Engine Technology By Turbine Panda
The hacking team targeted companies between 2010 and 2015, and successfully breached C919 suppliers like Ametek, Honeywell, Safran, Capstone Turbine, GE, and others.

But unlike in other Chinese hacks, where China used cyber-operatives from military units, for these hacks, the MSS took another approach, recruiting local hackers and security researchers.
The group, which Crowdstrike said it tracked as Turbine Panda, was extremely successful. The US cyber-security firm points out that in 2016, after almost six years of non-stop hacking of foreign aviation companies, the Aero Engine Corporation of China (AECC) launched the CJ-1000AX engine, which was set to be used in the upcoming C919 airplane, and replace an engine that a foreign contractor had previously manufactured.
FC-31 aircraft design and features

The medium-sized Shenyang J-31 fighter aircraft features diverterless supersonic inlet (DSI) design with bumps and forward-swept inlet cowls. The airframe incorporates a pair of low-aspect ratio trapezoidal planform wings with titanium spars. Each wing has a sweep of 35° and the stealthy design offers reduced radar cross-section (RCS).
Diverterless supersonic inlet (DSI) design

The bolts and wieldings are visible even after the dark-brown paints on the skin of aircraft which is an indication that Chinese engineers are still learning about meshed composite structure. The composites also rendering aircrafts with a smooth surface reducing radar cross section further.
The chined fuselage of the J-31 incorporates a pair of tailplanes. The rear edge of the fuselage is hinged with two vertical stabilisers. A rudder is installed on each stabiliser to control the aircraft’s movement. The aircraft is fitted with a tricycle landing gear. The nose landing gear consists of double wheels, while the main landing gear has a ‘dogleg’ structure.
Fourth-Gen Su-30MKI Can Detect J-20
The Indian Defence Research Wing says its Russian-made Su-30MKI fighter jets can spot the supposedly-stealth J-20s, and has already observed them in flight.
Indian Air Force Chief Marshal Birender Singh Dhanoa said the “Su-30 radar is good enough and can pick it (J-20) up from many kilometers away,” according to Indian news website Zee News.
India has been basing its Su-30MKIs in the northern part of the country to counter China’s deployments of J-20s, which struggle to take off in the high altitudes near Tibet, Zee News reported.
The Su-30MKI represents a new and effective Russian jet with an advanced array of radars that Justin Bronk, an air combat expert at the Royal United Services Institute told Business Insider could probably spot the J-20.
“It is entirely possible that the Su-30MKI can pick up track information on J-20 from quite long ranges,” Bronk said. “But what I would expect is that those tracks may be fairly intermittent and dependent on what headings the J-20 is flying on relative to the Sukhoi trying to detect it.”
Radar Cross Section
The Chinese use of materials to suppress frontal radar signature is interesting. Chinese Publications show that the Chinese are making a substantial investment in using materials to reduce radar signature and have produced large volumes of research results. So far, there have been no Chinese public disclosures on materials that substantially reduce signatures across a broad range of air combat radar frequencies.
On the Dubai Air Show, China admitted that FC-31 uses no baked meshed technology that makes the plane stealthy. Instead, China used mostly steel-aluminium alloy to build the airframe. A frontal radar absorbent material is used, and the airframe receives a paint scheme.
Chinese media is under the tight control of the communist party; outside media will never know what specific materials are used in FC-31 to manufacture the plane.
FC-31 in Zhuhai Airshow November 2016
 FC-31 Mock-up
FC-31 Mock-up
Naval variant J-31
 Naval FC-31
Naval FC-31
Following the first flight of a second Shenyang FC-31 prototype on December 23 last year, the Chinese media is now discussing whether the improved aircraft might be slated for operations on the new Chinese carrier fleet. The aircraft has been named the “Gryfalcon.”
Cockpit and avionics
The aircraft is operated by a single pilot. A transparent, two-piece canopy encloses the cockpit to provide increased visibility for the pilot.

Cockpit
 Mock-up cockpit of the J-31 as it was shown in public
Mock-up cockpit of the J-31 as it was shown in public
Display
The aircraft can be equipped with avionics, including multifunctional displays, helmet-mounted sight, an electro-optical targeting system (EOTS), an attitude director indicator (ADI), and advanced sensors and communication systems.

Prototype Helmet-mounted sight
EOTS-86 Electro-optical and sensor system
A privately-owned Chinese sensor company has unveiled a suite of prototype air-to-air and air-to-ground sensors in development for the latest Chinese and Russian fighters.

Wang Yanyong, technical director for Beijing A-Star Science and Technology, confirms that two systems – the EOTS-89 electro-optical targeting system (EOTS) and the EORD-31 infrared search and track (IRST) – are in development for China’s J-20 and J-31 fighters.
Both systems have completed ground testing in a laboratory, and are now ready to enter flight testing, he says. Chinese combat aircraft manufacturer AVIC is considering integrating the sensors on a testbed aircraft, then could decide to test them on the J-20 and J-31, he says.
Operational status is at least few years away for both sensors and possibly longer, Yanyong adds.
A-Star’s EORD-31 IRST
 . A-Star’s EORD-31 IRST uses a unique faceted sensor dome.
. A-Star’s EORD-31 IRST uses a unique faceted sensor dome.


Sensors
- Laser Target Designator & Ranger (LTD/R) – Range 18.5 KM surface only mode.
- A-Star’s EORD-31 appears to be a conventional infrared search and tracking (IRST) system but with a faceted sensor dome.
- BM/KJ-8602 [SPS-1000] (RW 1045) Radar Warning Receiver – Radar Warning Receiver (RWR) is designed to provide the pilot with real time and unambiguous threat warning over 360 degrees thus reducing vulnerability of the combat aircraft to radar associated weapons. Currently two different models of RWR are available i.e. BM/KJ-8602 RWR and BM/KJ-8602A RWR.
- Missile Approach Warning System – maximum range 9.3km
- Identification Friend or Foe (IFF) – Identification of Friend or Foe (IFF) system is solid state, airborne and selective transponder being co-produced in collaboration with M/s JIUZHOU China. It is used for identification of friend or foe. The system is compatible which civil ATC radar beacon system for air traffic control. PAC also provides the life cycle maintenance support to the JZ/YD 125 IFF system.
- Weapon Mission Management Computer – WMMC is a central computer for JF17 aircraft avionic system control and management. The basic tasks of WMMC are multiplex data bus communication management, mission planning and flight program management, fire control calculation, navigation assistance, audio alarming, integrated display managing (including digital map display control) and pilot interface control for avionics systems.
- All sensors and systems are the same as the Sino-Pac JF-17 fourth-generation fighters.
Armament of Shenyang FC-31
The Shenyang FC-31 fighter can be fitted with one internal cannon, two internal weapons bays in the fuselage and three payload hard-points on each of the two wings. Each internal weapons bay can accommodate up to two missiles including SD-10A BVRAAM and PL-10E externally.
Specifications of FC-31
The fighter jet has a length of 17.3m, height of about 4.8m, and a wing span of 11.5m. The empty weight is about 17t and the maximum take-off weight is 25t. The aircraft can carry out missions at medium and low-altitudes.



FC-31 Fighter Engines
The aircraft is powered by two RD-93 engine as the JF-17 and MiG-29. The RD-93 afterburning turbofan engines developed by Russian company JSC Klimov. Each engine generates an afterburning thrust of 84kN. The propulsion system also features fixed stealthy nozzles.
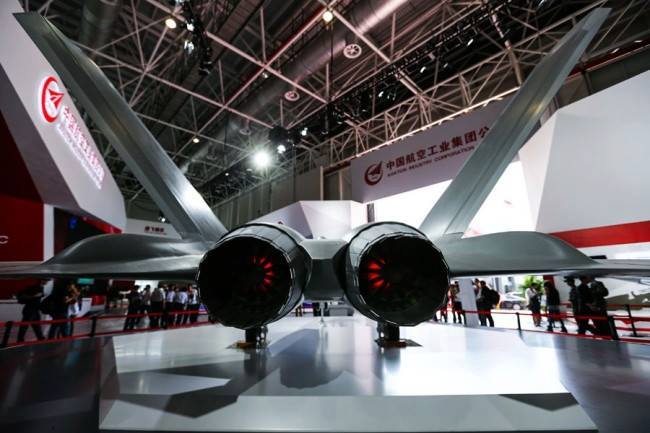
The aircraft can fly at a speed of approximately mach 2 and will offer a maximum range of over 2,000km when fitted with external fuel tanks. The service ceiling of the aircraft is approximately 20,000m.
The RD-93 is highly vulnerable to heat-seeking missiles and produces smokes which can be detected from long distance.
Latest Development

Chinese defence websites have published footage of what is apparently the second AVIC FC-31 Gyrfalcon fighter aircraft.
Still imagery shows the aircraft taking off. One major difference is the configuration of the aircraft’s twin canted tail. Produced by Shenyang Aircraft Corporation, the FC-31 features a cropped tail, whereas the first prototype designated J-31, had a nearly triangular tails with a horizontal top.
The J-20 and FC-31 are Chinese experiments in building a domestic fighter jet through espionage and intellectual property theft, but they are a long way from becoming stealth fighters.
© 2020 – 2024, GDC. © GDC and www.globaldefensecorp.com. Unauthorized use and/or duplication of this material without express and written permission from this site’s author and/or owner is strictly prohibited. Excerpts and links may be used, provided that full and clear credit is given to www.globaldefensecorp.com with appropriate and specific direction to the original content.










Be the first to comment